Documentation Index
Fetch the complete documentation index at: https://docs.hopae.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview
- Who is the user? → returned under
user. - How was this identity verified? → described by
provenance. - Did the user’s claimed values match the source? → returned under
matchfor match-capable providers.
Verification models
The top-levelverification_model field tells you which payload shape to read:
verification_model | When | Read from | user |
|---|---|---|---|
disclosure | The provider returned user attributes from an authoritative source. Default for all classic providers. | user.* (PII) and provenance | object with PII |
match | The provider compared RP-submitted values against the authoritative source and returned only a match outcome. | match.* and provenance | always null |
verification_model is always present. Verifications created before this field existed default to "disclosure". provider_id mirrors the single element in amr and is also always present.
For match-capable providers, matchData (the values the RP wants verified) must be supplied at session creation. The keys you submit appear back in match.submitted_fields. See Create Verification (matchData body field) and OIDC Authorization (match_request JWT param).
What “Provenance” Means
Provenance explains the verification story — who vouched for the identity, how it was presented, and when it happened.- Presentation
- Channel: the route and transport (for example,
centralized_idpoverinternet,chip_basedvianfc,walletoverinternet). - Credentials[]: the documents or assertions that were presented (
typeis the provider identifier, alongside issuer details and raw upstream claims). - Evidence (when provided)
- Evidence is included when the credential provides it; the object relays the upstream
tokenpayload and a semicolon-delimitednameslist describing the keys. Key names are provider-specific—always read them fromnames. Content is relayed from the credential source.
- Evidence is included when the credential provides it; the object relays the upstream
- Channel: the route and transport (for example,
- Metadata
- Verification identifiers and timestamps for audit and support (
verification_id,verified_at).
- Verification identifiers and timestamps for audit and support (
UserInfo Payload Structure
Here is a conceptual map of the UserInfo payload. This tree view shows how the data is organized, with a brief explanation for each major component. For detailed field specifications, refer to the Schema Tables that follow this section.Match payload example
A complete/userinfo response from a match-capable provider:
For match providers,
provenance.presentation.credentials[].claims carries the upstream IDP response verbatim — typically per-field confirmation from the source authority. This is the audit trail for what the source agreed with — it is not a duplicate of match.details.details may include keys that are not in submitted_fields when the upstream provider emits additional verifier results (e.g., a liveness signal alongside the demographic match outcome).Related
Next Steps
OIDC Provider
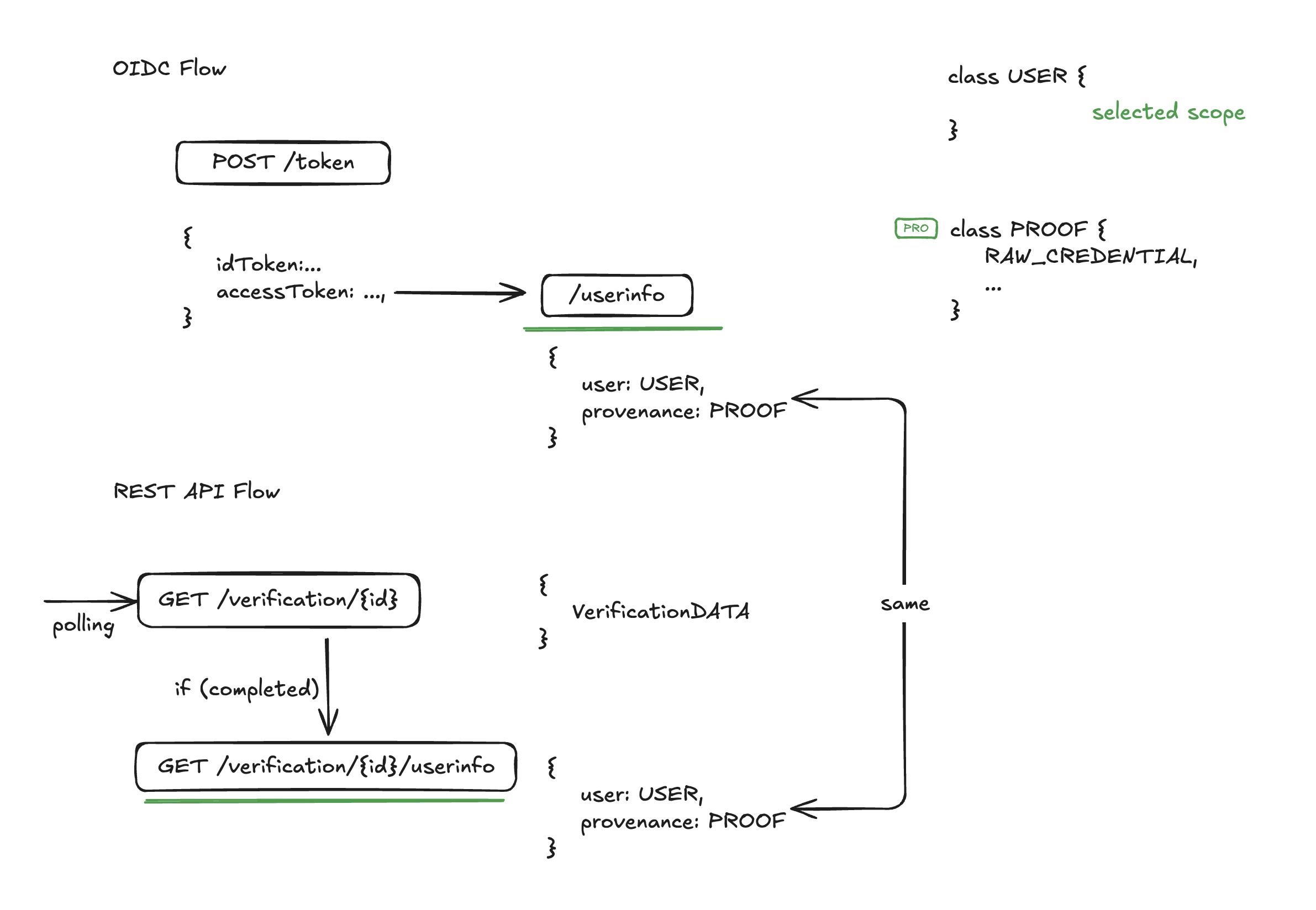
How OIDC fits into User Verification
Verification Flow
Understand the end-to-end lifecycle